How to Audit a Smart Contract (Without Being a Developer)

Last Updated: April 2026
I'll be honest with you. The first time
someone told me to "check the audit" before investing in a DeFi
project, I nodded like I knew what that meant.
I didn't.
I clicked the link they sent me, stared
at a PDF full of Solidity code and words like "reentrancy" and
"integer overflow," and closed it within 45 seconds. Completely
useless to me.
Here's what I've figured out since then:
you don't have to understand the code to get real value from a smart
contract audit. You just have to know what you're actually looking for —
and what red flags mean something's wrong even if you can't read a single line
of the contract itself.
That's what this guide is. Not a developer tutorial. A practical breakdown for regular people who want to stop nodding and actually understand what they're looking at.

First — What Is a Smart Contract Audit, Actually?
A smart contract is code that runs
on a blockchain automatically when certain conditions are met. No humans needed
to execute it. It handles the rules of a DeFi protocol — who can withdraw
money, when, how much, under what conditions.
A smart contract audit is when an
independent security firm goes through that code before it launches (and
sometimes after) looking for problems. Not typos. Real problems — logic flaws,
ways an attacker could drain the protocol, backdoors a developer could use to
steal funds.
Think of it like a home inspection before
you buy a house. You're not doing the inspection yourself. But you read the
inspector's report and decide if the issues they found are dealbreakers.
That's your job here.
Why This Matters More Than You Think
In 2025 alone, over $3.4 billion was lost
to smart contract exploits and hacks. Not all of it from unaudited code — some
of the biggest losses came from protocols that had been audited and
still failed.
The $1.4 billion Bybit hack in February
2025 is the clearest example. The attack wasn't even in the smart contract
code. It was in the signing infrastructure — the off-chain tools
developers used to approve transactions. The audit covered the contract. It
didn't cover the full system. That gap cost users $1.4 billion.
And the $223 million Cetus Protocol loss?
That one was audited too. The issue was a concentrated-liquidity math error
that formal verification would have caught — but a standard code review missed.
So audits matter. But they're not magic. Knowing the difference between a thorough audit and a checkbox audit is something anyone can learn.

What a Smart Contract Security Review Actually Checks
When a firm does a smart contract
security review, they're looking at several layers. You don't need to
understand the code. But you should know these categories exist and what they
mean when flagged.
Access Control (SC01)
This is the #1 source of losses in 2025 —
$953.2 million drained from access control failures alone. It means: who can
call which functions? If an admin function doesn't require the right
permissions, an attacker (or a malicious developer) can call it and drain
funds.
What to look for in a report: any
"Critical" or "High" finding mentioning "unauthorized
access," "missing modifier," or "privileged role."
These are not minor issues.
Business Logic Flaws (SC02)
This one is sneaky. The code runs exactly
as written — but the way it's written breaks the economic rules of the
protocol. Maybe there's a way to borrow more than your collateral should allow.
Maybe a rounding error means attackers can extract tiny amounts repeatedly
until the pool is empty.
Business logic flaws require a manual
review against the project's whitepaper. Auditors call this a
"Specification Review" — they check if the code actually does what
the documentation says it does.
Price Oracle Manipulation (SC03)
Most DeFi protocols need real-time price
data. They get it from external services called oracles. If a protocol relies
on a single price source, an attacker can temporarily manipulate that price —
usually through a flash loan — and exploit the distorted reading to drain
funds.
Good audit reports flag single-oracle
dependence. Good protocols use decentralized feeds like Chainlink with circuit
breakers that pause the system if prices move too fast.
Flash Loan Attacks (SC04)
A flash loan is a loan borrowed and
repaid within a single transaction. No collateral needed. An attacker can
borrow tens of millions of dollars, use that money to manipulate a protocol's
logic, and repay it — all in one block.
Flash loan vulnerabilities aren't always
obvious in the code. They require economic stress-testing, not just code
review. If an audit report doesn't mention flash loan scenarios, that's worth
noting.
Reentrancy
This is the granddaddy of DeFi
vulnerabilities. It's how the DAO hack happened in 2016. Basically, an attacker
calls a withdrawal function, and before the contract updates the balance, the
attacker calls it again — and again — draining funds in a loop.
A good audit checks for this specifically. If a report mentions reentrancy and marks it "Acknowledged" without a fix, that's a problem.
How to Read a Smart Contract Audit Report (Without the Code)
Here's the part most guides skip. Let me
walk you through it.
Step 1: Find the Executive Summary
Every legitimate audit report starts with
one. It tells you the scope of what was reviewed, the dates, the commit hash
(the specific version of code that was reviewed), and a summary of findings.
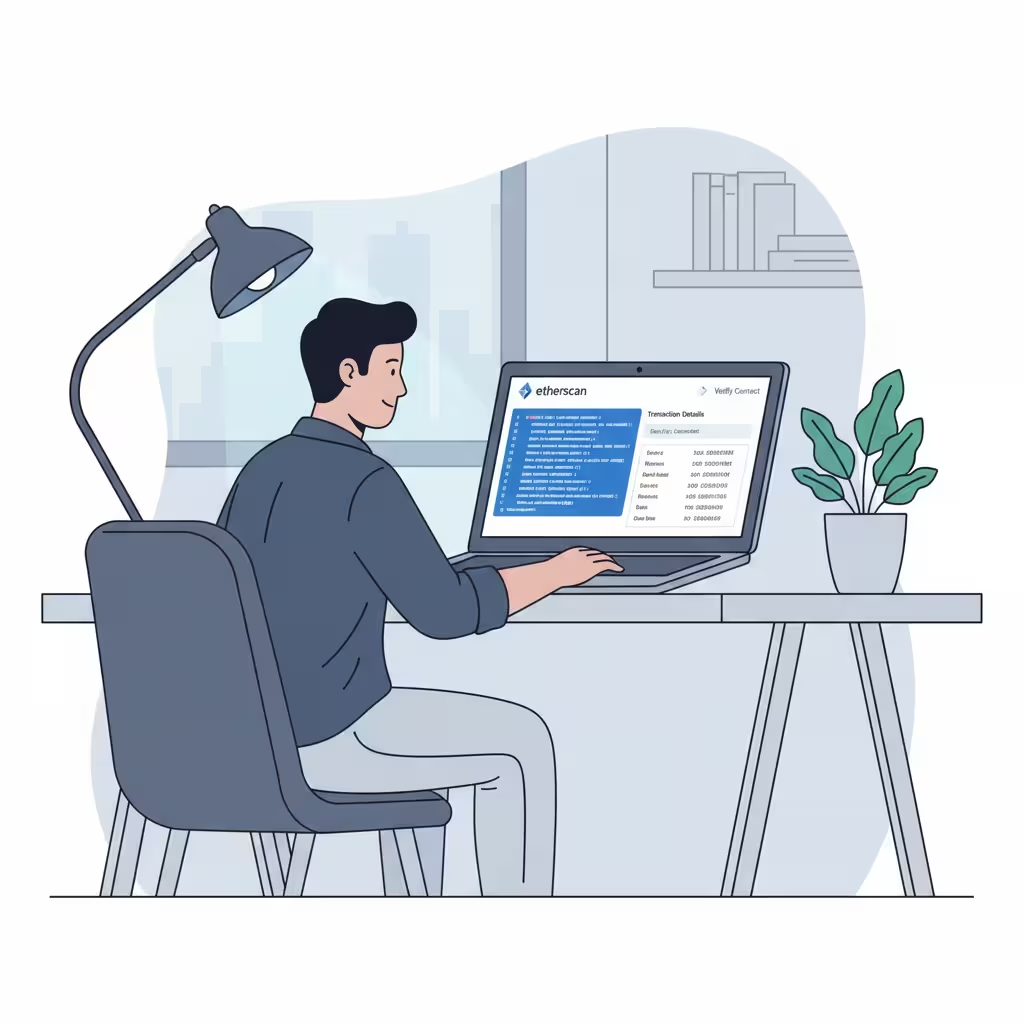
Check the commit hash. It should match
what's actually deployed on-chain. If a project got audited but then changed
the code before launch, the audit is worthless. You can verify deployed
contract code on Etherscan or similar block explorers.
Step 2: Look at the Severity Breakdown
Audit findings come in categories:
●
Critical — Assets are at immediate risk. Fix required before launch, full stop.
●
High —
Exploitable under specific conditions. Fix mandatory before mainnet.
●
Medium
— Could lead to logic failure. Should be fixed.
●
Low —
Minor inefficiencies, not urgent.
●
Informational — Style or documentation suggestions.
What you care about: Were there any
Critical or High findings? If yes — what was the resolution?
Step 3: Check the "Action
Taken" Column
This is the most important column in the
whole report, and most people ignore it.
Every finding should show what the
development team did in response. The options are usually "Fixed,"
"Acknowledged," or "Disputed."
"Fixed" is what you want.
"Acknowledged" means they know about it and chose to leave it.
"Disputed" means they disagree it's a vulnerability. Both of those
deserve a closer look. A protocol with two Acknowledged High-severity issues is
a different risk profile than one where everything was fixed.
Step 4: Check Who Did the Audit
Not all auditing firms are equal. In
2026, the established names in the space include Trail of Bits, OpenZeppelin,
Spearbit, Sherlock, and Code4rena for contest-based reviews.
Be skeptical of audits from firms you've
never heard of. Some projects pay for audits from low-cost shops that do
minimal work and produce reports that look official but aren't. A real audit
from a credible firm for a standard DeFi protocol costs between $50,000 and
$100,000 and takes three to six weeks. If a project claims they got a thorough
audit done in two days for $500, that's a red flag.
Step 5: Check the Date
An audit from 2021 means nothing for a
protocol running in 2026. The code may have changed a dozen times. New
vulnerabilities are discovered constantly. The 2026 OWASP Smart Contract Top 10
identifies attack patterns that didn't exist five years ago.
If the most recent audit is more than 12 months old and the protocol has released major updates since then, treat it as unaudited.
How Much Does a Smart Contract Audit Cost?
This comes up constantly, so here are the
real 2026 numbers.
Audit pricing has moved away from
per-line-of-code pricing to what's called Logic Density Valuation —
pricing based on the complexity of what the code does, not how many
lines it takes to do it.
A 500-line zero-knowledge verifier is
exponentially more complex to audit than 5,000 lines of standard token code.
The auditor has to understand every possible state the code can reach, every
interaction with other contracts, every edge case.
Here's a rough breakdown:
|
Protocol
Type |
Typical
Cost |
Typical
Duration |
|
Basic ERC-20 token or NFT |
$15,000 – $25,000 |
2–5 days |
|
DEX, lending, staking protocol |
$50,000 – $100,000 |
3–6 weeks |
|
Cross-chain bridge or ZK rollup |
$150,000 – $500,000+ |
2–6 months |
If you see a new DeFi
project claiming a full audit of their lending protocol for under $10,000,
something is off. Either the audit wasn't thorough, the firm isn't credible, or
the scope was limited to a small part of the codebase.

How to Verify if a DeFi Contract Is Audited (Step by Step)
So the project says they've been audited.
Here's how to actually check.
Check their documentation or GitHub. Legitimate audits are published publicly. If a project claims an audit
but won't share the report, that tells you everything.
Cross-reference on Etherscan. Search the contract address on Etherscan. Under the
"Contract" tab, check if the code is verified. Verified means the
source code is public and matches what's deployed. If it's not verified, you
can't even compare the audit to the live code.
Check the audit firm's website
directly. Some firms publish their completed audits on
their own site. Trail of Bits, OpenZeppelin, and Spearbit all do this. If the
project says CertiK audited them, look it up on CertiK's own platform, not just
the project's marketing page.
Check the date and commit hash. Already covered above but worth repeating. The commit hash in the
audit report should match what's on Etherscan.
Look for a bug bounty program. This is a sign of ongoing security commitment. Platforms like Immunefi run active bug bounty programs where researchers earn rewards for finding vulnerabilities. A project with an active bounty has skin in the game. By 2025, crypto insurance tied to active bounty programs reached $9.5 billion in coverage — that's how seriously institutional players take this.
The Best Smart Contract Auditing Tools Exist — But They're Not for You
You'll read about tools like Slither,
Echidna, Mythril, and the Certora Prover. These are real, they're used by real
auditors, and they're genuinely powerful.
Slither does static analysis — fast
detection of common vulnerability patterns. Echidna does fuzzing — throwing
thousands of random inputs at a contract to see what breaks. The Certora Prover
does formal verification — using mathematical proofs to confirm the code can
never violate its core rules.
You don't need to run these. But knowing they exist helps you ask better questions. Did the audit use only static analysis tools? Did it include fuzzing? Was formal verification done? Higher-assurance audits layer multiple methodologies. Basic ones run one tool and call it done.
One Thing Non-Developers Get Wrong
People assume that if a protocol has been
audited, it's safe. That's not how this works.
Even audited code has failed. Multiple
times. At massive scale. The Cetus Protocol had an audit. Balancer v2 had
audits. Both lost enormous amounts of money to vulnerabilities that either
weren't found or weren't fixed.
An audit reduces risk. It doesn't
eliminate it. The right question isn't "was this audited?" It's
"what did the audit find, how old is it, who did it, and what happened to
everything they flagged?"
Those five questions will tell you more than any audit badge on a project's homepage.
Frequently Asked Questions
How to read a smart contract audit
report without coding knowledge? Focus on the
executive summary, severity breakdown, and the "Action Taken" column
for every finding. Critical and High findings that were
"Acknowledged" instead of fixed are warning signs that don't require
code knowledge to recognize.
What does a smart contract audit check
for? Audits check for access control failures,
business logic flaws, price oracle manipulation, flash loan vulnerabilities,
reentrancy attacks, and integer overflow errors. The 2026 OWASP Smart Contract
Top 10 is the current industry standard for what comprehensive audits cover.
How much does a smart contract audit
cost in 2026? Standard DeFi protocols (DEXes, lending,
staking) cost between $50,000 and $100,000 and take three to six weeks. Basic
token contracts run $15,000 to $25,000. High-complexity infrastructure like
cross-chain bridges can exceed $500,000.
What are the best smart contract
auditing firms in 2026? Trail of Bits, OpenZeppelin,
Spearbit, and Sherlock are among the most respected. Immunefi runs the largest
bug bounty platform. Code4rena and Sherlock run competitive audit contests for
large codebases.
How to verify if a DeFi contract is
audited? Check for a publicly available audit report,
verify the contract source code on Etherscan, confirm the commit hash in the
report matches the deployed code, look up the audit on the firm's own website,
and check when the audit was completed relative to any major code updates.
What is a reentrancy attack in simple terms? It's when an attacker exploits a withdrawal function by calling it repeatedly before the contract updates the balance — essentially looping a withdrawal to drain funds. The 2016 DAO hack used this method and it remains on the 2026 OWASP Top 10 today.
The Bottom Line
You don't need to read Solidity. You
don't need to understand the EVM. You don't need to run fuzzing tools on your
own machine.
What you need is to know what questions
to ask and what the answers should look like. Who audited it. When. What they
found. What got fixed. Whether the code that's actually running matches what
was reviewed.
That's it. That's the whole job for a
non-developer doing smart contract due diligence.
The $3.4 billion lost in 2025 didn't
disappear because people couldn't read code. A lot of it disappeared because
people didn't check — or they checked the wrong things, or they trusted a badge
on a homepage without clicking through to the actual report.
Do the five checks above before you put
money into anything. Every time.
Disclaimer: This article is for informational purposes only and does not constitute financial or legal advice. Smart contract investments carry significant risk including total loss of funds. Always conduct your own research before investing